Most Civilian Agency Cybersecurity Programs Are Ineffective, says GAO
Published: January 21, 2022
Federal Market AnalysisCybersecurityGAOPolicy and Legislation
Roughly 70% of federal civilian agency cybersecurity programs are ineffective, according to a recent government review.
This year marks the twentieth anniversary of the Federal Information Security Management Act (FISMA) of 2002. FISMA required each federal agency to develop an agency-wide information security program to protect their information and systems. Congress updated the law in 2014 to bolster federal capabilities to respond to increasing cyber-attacks upon agencies. However, recent evidence from the U.S. Government Accountability Office (GAO) portrays the effectiveness of agencies’ efforts to be uneven at best, highlighting the ongoing struggle that agencies have with implementing effective cybersecurity and how to best measure effectiveness.
Civilian Agency Cybersecurity Programs Struggle to Meet Effectiveness Standards
Recently, the U.S. House Committee on Oversight and Reform (COR) held a hearing to examine strategies to strengthen FISMA. Among those testifying was Jennifer R. Franks, Director of Information Technology and Cybersecurity at GAO. In her testimony Franks discussed GAO’s key findings of their ongoing review of agency implementation of FISMA, including the effectiveness of federal agencies’ implementation of cybersecurity policies and practices as assessed by agency inspectors general (IGs).
The results show that the effectiveness of federal agencies’ implementation of FISMA requirements varied from year to year, from agency to agency and by cybersecurity capability.
Effectiveness is assessed by how well agencies measure against 10 targets addressing cybersecurity associated with software asset management, hardware asset management, authorization management, mobile device management, privileged network access management, high-value asset access management, automated access management, intrusion detection and prevention, exfiltration and enhanced defenses, and data protection.
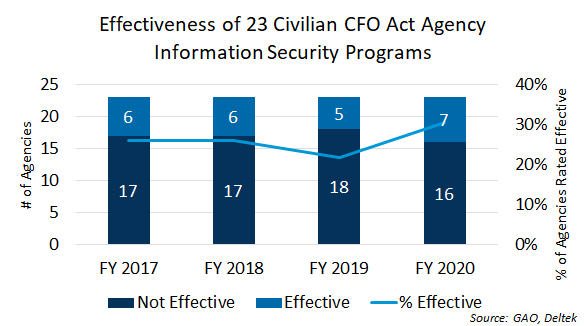
For fiscal year (FY) 2020, agency IGs determined that seven of the 23 civilian agencies covered under FISMA (i.e. agencies covered under the Chief Financial Officers Act of 1990, a.k.a. CFO Act agencies) had effective agency-wide information security programs. The results for FY 2017 to FY 2020 were similar with a slight increase for FY 2020. (FISMA results for FY 2021 are not expected to be published until half-way through FY 2022. Past reports have often come in March, but the last few years it has stretched to May and even August.)
These assessments rate the level of effectiveness among civilian agencies from FY 2017 to FY 2020 to be between 22% to 30%, averaging 26%, with a decline showing in FY 2019 and a rebound in FY 2020. (See chart below.)
The IGs identified uneven implementation of cyber security policies and practices as a major issue. GAO notes that of the 3,700 cybersecurity recommendations it has made to agencies since 2010, about 900 were not yet fully implemented as of November 2021.
The challenge and urgency agencies have with implementing effective cybersecurity is further underscored by the sustained level of cybersecurity incidents reported by agencies to the U.S. Computer Emergency Readiness Team (US-CERT).
The news is not all bad. According to GAO, in FY 2020 more agencies reported meeting capability goals for cybersecurity incident detection and prevention (18 of 23) and for goals for access management (19 of 23). Nevertheless, 16 of the 23 agencies did not meet all 10 of the federal cybersecurity targets in FY 2020.
Challenges and Recommendations from Agencies
While agency officials such as Chief Information Officers (CIO) and Chief Information Security Officers (CISO) at all 24 CFO Act agencies (Defense included) told GAO that FISMA and its related reporting process had helped their agencies improve their security posture, they also cited challenges to implementing FISMA, including lack of sufficient resources, the compliance- vs. effectiveness- nature of FISMA reviews, and the time crunch associated with implementing new requirements or remediation actions identified in the previous FISMA review before the next review starts.
Agency officials also suggested several ways to improve the FISMA reporting process to increase its effectiveness impact on cybersecurity, including updating FISMA metrics, shifting its focus from compliance to operational risk, increased automation, introducing a graduated maturity-rating scale into the IG evaluation process, and reducing the frequency of FISMA-mandated IG audits to reduce the burden of the annual review cycle.
The Office of Management and Budget (OMB) has begun working to implement many of these suggestions in their latest annual FISMA guidance to agencies published in December. Specifically, OMB is working to shift the emphasis from compliance to risk management, emphasize automation, and formulate a new reporting cycle for FISMA metrics.
Potential Updates to FISMA Coming from Congress
Congress has been looking at ways to again update FISMA to address the challenge. Last September, legislation was introduced in the Senate to update FISMA, including agency cyber incident reporting and information sharing requirements, but the bill did not advance. For its part, the House COR has now released a draft FISMA update bill of its own that seeks to clarify federal cybersecurity roles, promote a risk-based cybersecurity posture, modernize and streamline reporting, expand system and software inventories and incident information sharing, and promote cybersecurity shared services and agency technical support. Several of these priorities support elements of the May 2021 White House Executive Order on cybersecurity.
Time will tell whether or not FISMA modernization will rise to the top of legislative priorities in this Congress. Stay tuned.
_____
Get our assessment of the federal cybersecurity market in our report, Federal Information Security Market, 2021-2023.