OMB Cybersecurity Metrics Show Agencies Still Struggle to Report Effectively
Published: September 23, 2022
Federal Market AnalysisCybersecurityCISAOMBPolicy and Legislation
The latest federal information security status report shows both improvements and challenges agencies have with incident reporting.
Cybersecurity remains among the highest federal technology priorities, as the White House, the Office of Management and Budget (OMB), the Cybersecurity and Infrastructure Security Agency (CISA) and other federal agencies have taken numerous steps to protect federal IT systems and data in the face of persistent and adapting security threats. OMB’s latest Fiscal Year 2021 Federal Information Security Modernization Act of 2014 (FISMA) Annual Report to Congress reflects the continued challenge agencies face in both the variety of threats and their internal processes for classifying and reporting these incidents.
Reported Federal Cyber Incidents
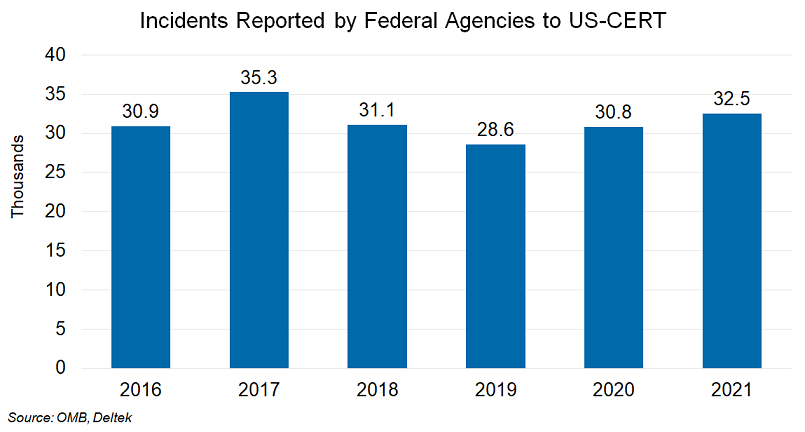
According to the latest OMB FISMA release, agencies reported 32,543 incidents cybersecurity incidents to the U.S. Computer Emergency Readiness Team (US-CERT) in FY 2021 – up 1,702 (+6%) compared to the 30,819 reported in FY 2020 and 3,962 (+14%) above the 28,581 reported in FY 2019. This marks the second year in a row that agencies have reported increases in incidents, reversing a declining trend in FY 2018 and FY 2019. The FY 2021 reported incident rate was exceeded only by the number reported for FY 2017, underscoring the existence of diverse and persistent threats. (See chart below.)
Consistent Attack Vector Metrics for FY 2021
While OMB has swapped out over the years a couple of the smaller Attack Vectors that agencies were to report as part of their FISMA submissions, the current list has been consistent since FY 2018. The US-CERT guidelines break down incidents into the following nine Attack Vectors as described:
- Attrition – Employs brute force methods to compromise, degrade, or destroy systems, networks, or services.
- E-mail/ Phishing – An attack executed via an email message or attachment.
- External/Removable Media – An attack executed from removable media or a peripheral device.
- Impersonation/Spoofing – An attack involving replacement of legitimate content/services with a malicious substitute.
- Improper Usage – Any incident resulting from violation of an organization’s acceptable usage policies by an authorized user, excluding the other categories.
- Loss or Theft of Equipment – The loss or theft of a computing device or media used by the organization.
- Web – An attack executed from a website or web-based application.
- Other / Unknown – An attack method does not fit into any other vector or the cause of attack is unidentified.
- Multiple Attack Vectors – An attack that uses two or more of the above vectors in combination.
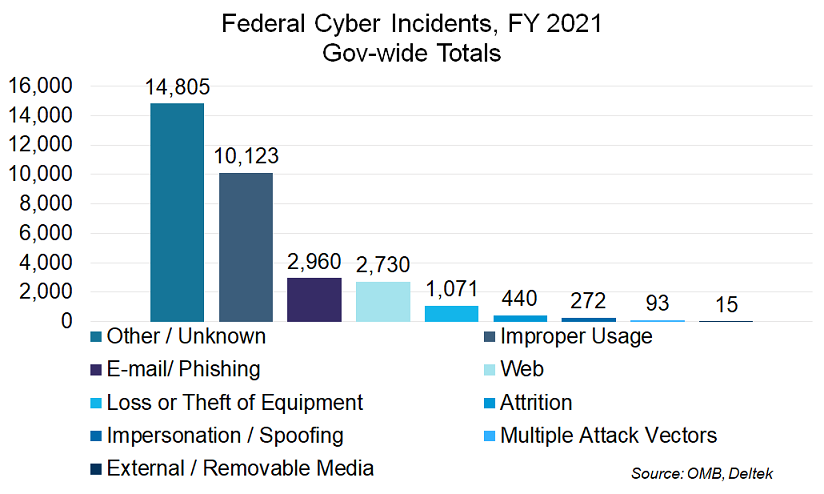
For FY 2021 these incidents break out across the nine Attack Vectors as follows, with the largest number falling into the Other/Unknown category. (See chart below.)
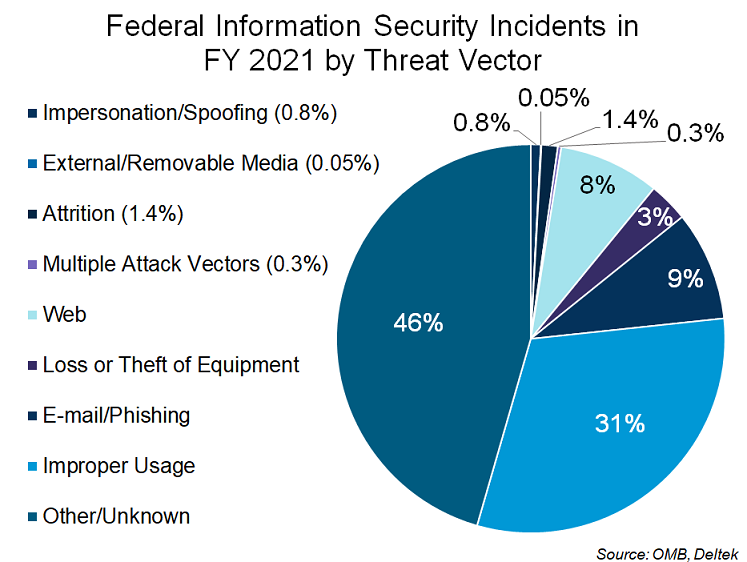
An alternative view of the FY 2021 cyber-incidents is to relate the relative frequency of each Attach Vector to the whole. (See chart below.)
Year-to-year changes from FY 2020 to FY 2021 in the frequency of the top Attack Vectors reveals the areas where agencies continue to experience some of the greatest challenges and where they have gained some ground.
In FY 2021, the Other/Unknown vector accounted for the highest number (14,805) and proportion (46%) of reported incidents, indicating that federal agencies are challenged to appropriately categorize incident vectors during reporting or fail to update their initial reporting once more clarity is gained during their investigation. Compared to the 10,102 incidents reported for FY 2020, the FY 2021 level represents a 47% year-to-year increase.
The FY 2021 data also indicates that agencies continue to struggle with Improper Usage (IU) violations by authorized users as it accounts for 31% of incidents. This vector has consistently remained near or at the top of the frequency list each year since FY 2018. That said, overall Improper Usage violations decreased by 15% from FY 2020 to FY 2021. Given that IU incidents result from an authorized user’s violation of their organization’s acceptable usage policies (excluding actions captured by other incident categories) the significant year-to-year decrease may indicate that agencies are making some headway in their user cyber training and education efforts.
Another bright spot, at 2,960 incidents (9%) in FY 2021, E-mail/Phishing has declined for the fourth straight year since FY 2017, most likely due to a combination of greater user awareness and security training and agency efforts to improve email and web security. Similarly, incidents related to External/Removable Media declined by more than half, indicating stricter usage policies, safer user behavior, deployment of alternative solutions, or even the increase in remote telework.
In contrast, Web-based incidents remained relatively flat/sustained in FY 2021, after a nearly 40% jump in FY 2020. Further, Attrition brute force attacks grew by nearly 30% in FY 2021. Although a relatively small proportion of reported incidents, its growth underscores the persistence of this threat vector. (See chart below.)
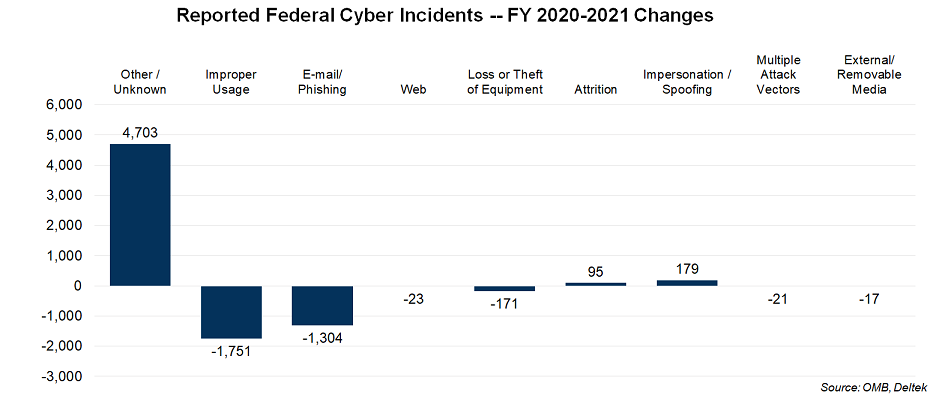
After significant attention and effort by OMB, CISA and individual agencies in the wake of several major cyber breaches in 2020 and 2021, both the frequency and increase of the Other/Unknown attack vector remains a concerning trend. The previous FY 2020 FISMA report revealed a 40% increase in this category from the 7,240 incidents reported for FY 2019. Incidents reported under the Other/Unknown category had been steadily and significantly decreasing from FY 2016 through FY 2019.
In their latest FISMA report OMB acknowledges the issue and pledges to keep working at it: “The prevalence of this attack vector suggests additional rigor must be applied by agencies to appropriately categorize the vector of incidents during reporting, and when applicable, update the initial report when the vector is unveiled during the investigation process. OMB and CISA continue to work with agencies to improve the quality of incident reporting data.”
This statement is not substantively different from what OMB said in last year’s report regarding the frequency and growth of the Other/Unknown category. Time will tell whether and when their efforts will help agencies turn the tide.